| Title | Author | Created | Published | Tags |
|---|---|---|---|---|
| Windows Vulnerability Exploited with Braille Spaces | Jon Marien | January 16, 2025 | - | - |
Overview:
- Vulnerability: Windows MSHTML Spoofing (CVE-2024-43461)
- Exploited by: Void Banshee APT group
- Targets: Organizations in North America, Europe, Southeast Asia
- Objective: Install information-stealing malware
Attack Details:
- Zero-Day Attacks: Used to deploy the Atlantida info-stealer
- Data Stolen: Passwords, authentication cookies, cryptocurrency wallets
- Methodology:
- Utilized Windows Internet Shortcut files (.url) to open malicious sites in Internet Explorer
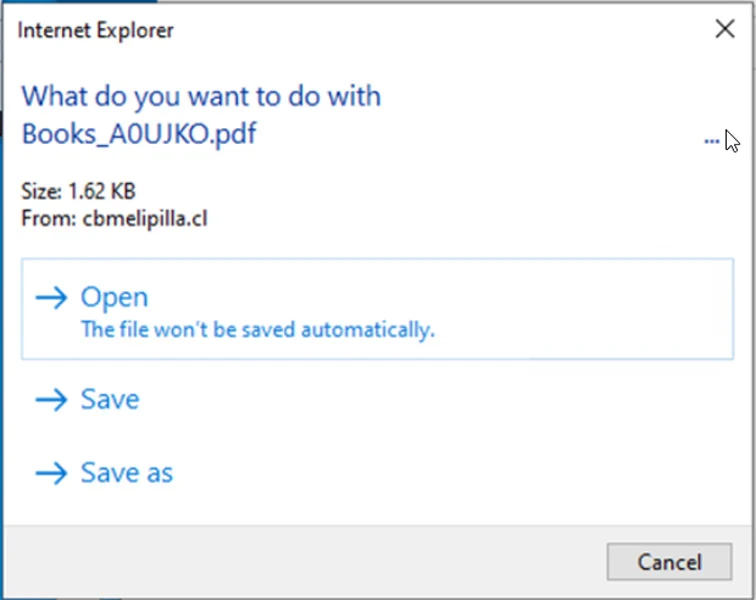
- Downloaded malicious HTA files disguised as PDFs using braille whitespace characters
Technical Exploit:
- Braille Whitespace Characters: Encoded as
%E2%A0%80- Used to hide the
.htaextension, making files appear as PDFs - Exploits a CWE-451 condition to deceive users
- File appears as PDF in Windows prompts
- Example filename:
Books_A0UJKO.pdf[26 braille spaces].hta - Windows shows “Books_A0UJKO.pdf…” hiding true extension
- Used to hide the
Mitigation:
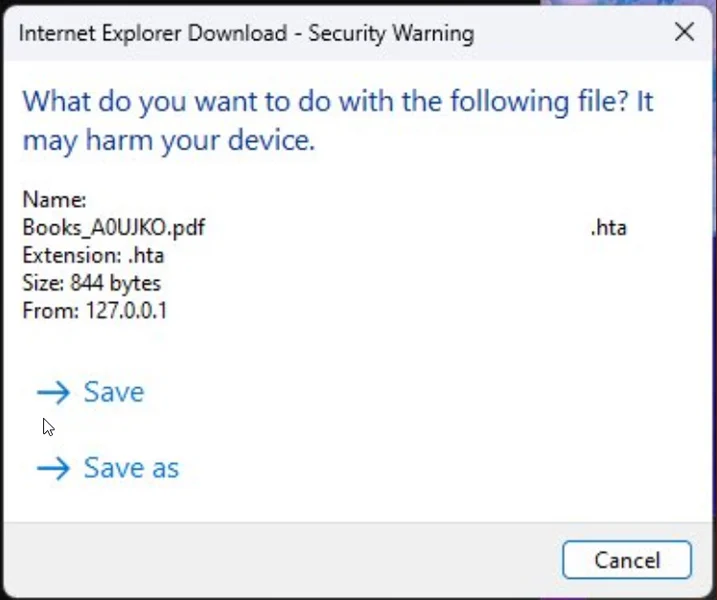
- Patch Released: September 2024 Patch Tuesday
- Fixes CVE-2024-43461 by displaying the actual
.htaextension - Not perfect; whitespace may still mislead users
- Fixes CVE-2024-43461 by displaying the actual
Highlight ”…” dots in photo:
Fixed prompt:
Presenter Notes
Presenter Notes:
- The attack uses 26 encoded braille whitespace characters (%E2%A0%80).
- Full filename example:
Books_A0UJKO.pdf%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80%E2%A0%80.hta - CWE-451 refers to User Interface (UI) Misrepresentation of Critical Information.
- This technique exploits how Windows handles long filenames in its user interface.
- The ’…’ in Windows prompts further obscures the true file extension.