| Title | Author | Created | Published | Tags |
|---|---|---|---|---|
| YouTube Malware Exploitation Campaign |
| January 15, 2025 | January 15, 2025 |
|
YouTube Malware Exploitation Campaign
Attack Overview
- Cybercriminals are using YouTube to distribute malware, bypassing traditional antivirus detections.
- They’re hijacking established YouTube channels, some with hundreds of thousands of subscribers, to spread info-stealing malware.
Malware Distribution Method
- Compromised channels upload videos offering free versions of premium software or game cheats.
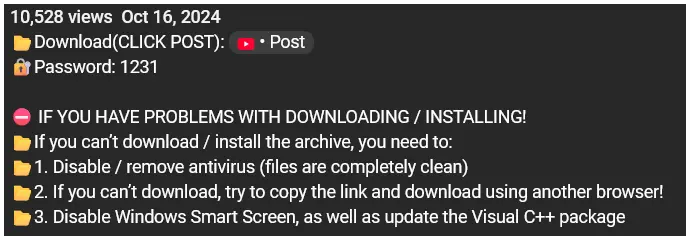
- Malicious download links are placed in video descriptions or comments, with password-protection.
- Attackers use legitimate file-hosting services like Mediafire and Mega.nz to host malware.
Advanced Techniques
- File Protection:
- Password-protected archive files (e.g., ZIP, RAR)
- Passwords provided in video descriptions or comments
- File Encoding:
- Use of Base64 encoding to obfuscate malicious code
- Makes it harder for antivirus software to detect threats
- URL Shortening:
- Employ services like TinyURL to mask full malicious URLs
- Hides true destination, exploiting users’ trust in short links
Malware Characteristics
- The primary malware is a variant of Lumma Stealer, a sophisticated information-stealing trojan.
- It can harvest sensitive data including:
- Saved passwords and autofill data from browsers.
- Cryptocurrency wallet information.
- Steam and Discord tokens.
- Credit card details.
- Desktop screenshots.
Protection Measures
To stay safe, you should:
- Avoid downloading cracked or pirated software.
- Be cautious of videos promising free premium software.
- Verify the legitimacy of download sources.
- Keep your antivirus software updated.
- Use additional security layers like web filtering.
Notes - For Speaker
- Traditional antivirus software often struggles to detect threats hosted on reputable platforms.
- They also seeded Google search results with links to fake software installers hosted on these platforms.
- Some campaigns employed steganography to hide malicious code within seemingly benign image files hosted on these services.
- Attackers took advantage of users’ familiarity with and trust in these well-known services.
- The use of legitimate platforms made malicious downloads appear more credible.