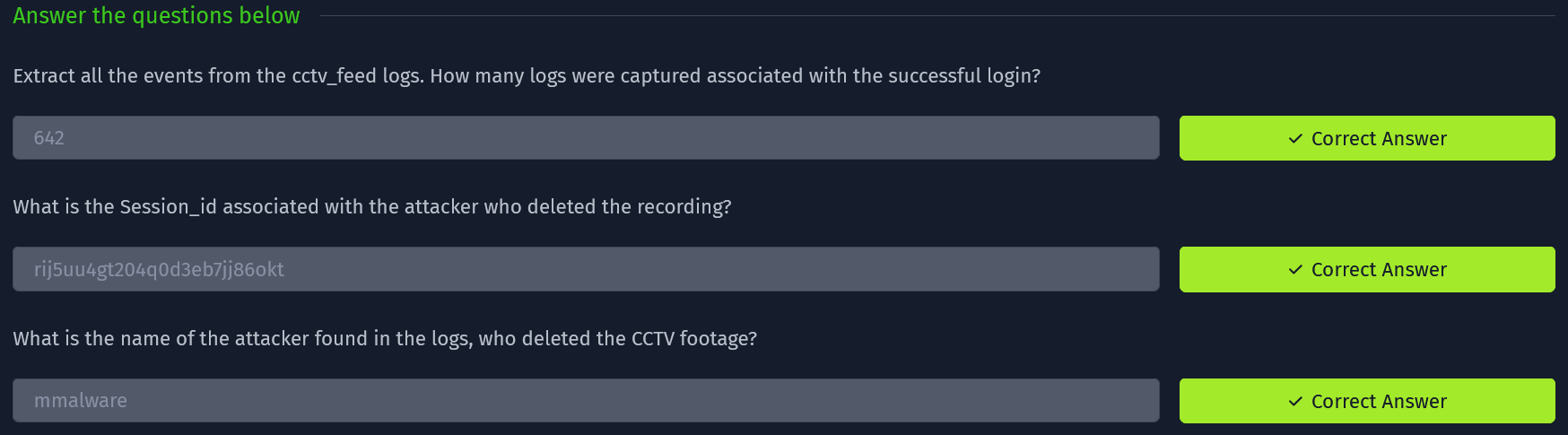
Log Analysis with Splunk!
I’ve already done half of the room, but wanted to have some pictures to refer to.
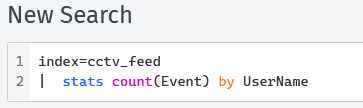
CCTV Feed by UserName
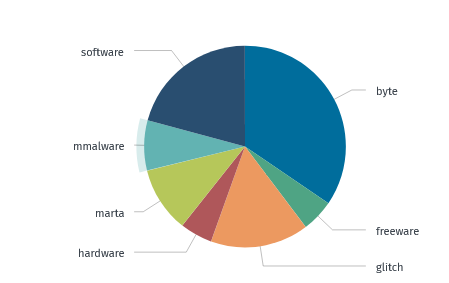
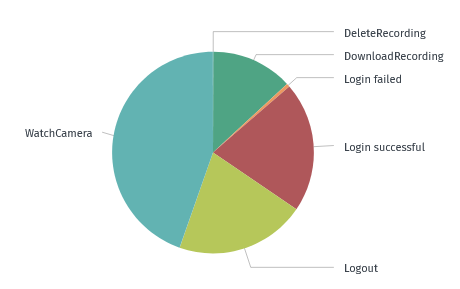
CCTV Feed by Event Type
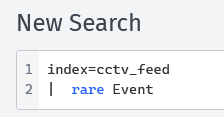
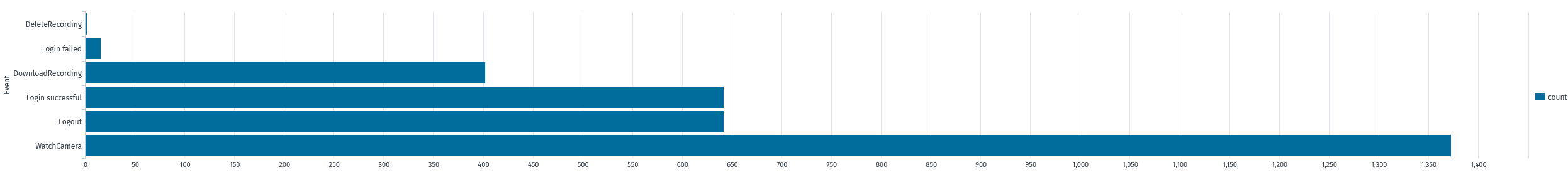
CCTV Feed by Rare Event
CCTV Failed Feeds, sorted by username with session_id’s
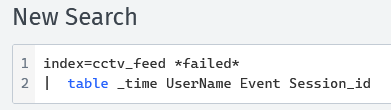
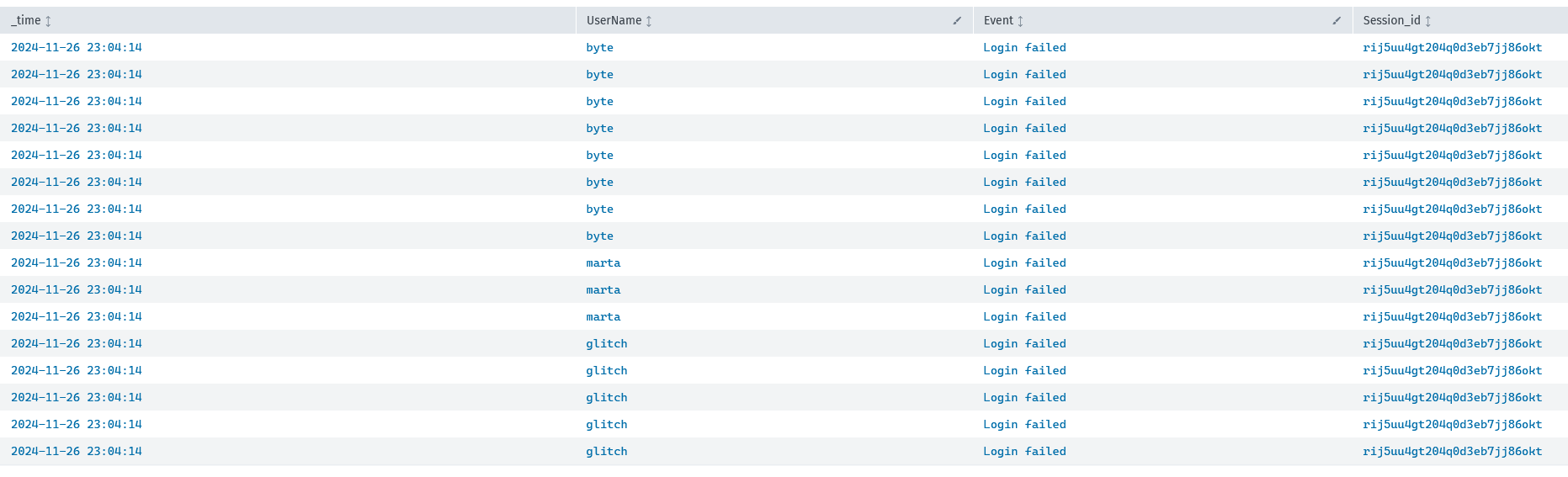 Even though the users are the same, it’s all originating from the same
Even though the users are the same, it’s all originating from the same session_id. Let’s search that session_id specifically!
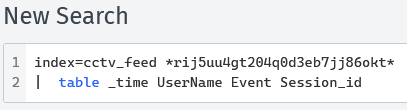
 It looks like he was trying to login, was failing, and finally succeeded. Then they proceeded to Watch and Delete Recordings. Let’s see which ones he accessed.
It looks like he was trying to login, was failing, and finally succeeded. Then they proceeded to Watch and Delete Recordings. Let’s see which ones he accessed.
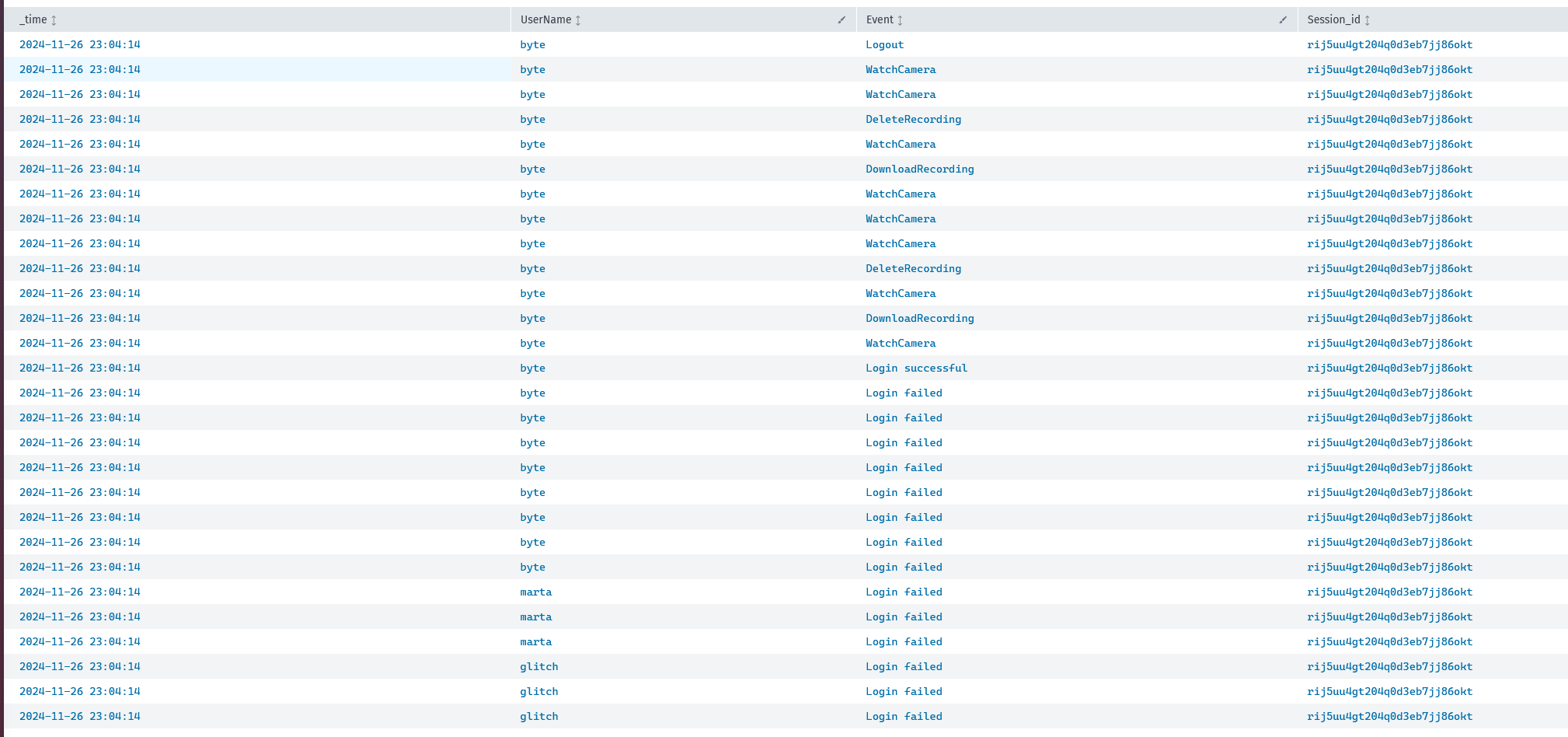
 We can take the
We can take the DeleteRecording session_id and search that! Let’s do that now.
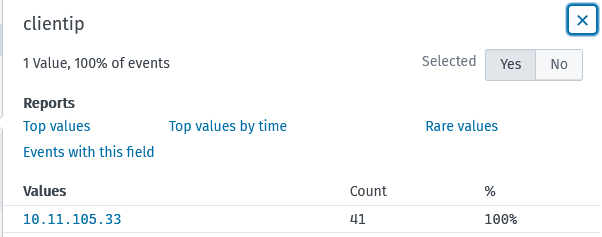
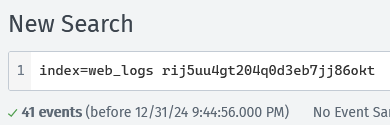 If we check the
If we check the clientip field within these results, we can see that there is only one IP!
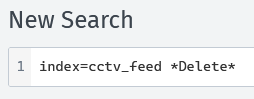
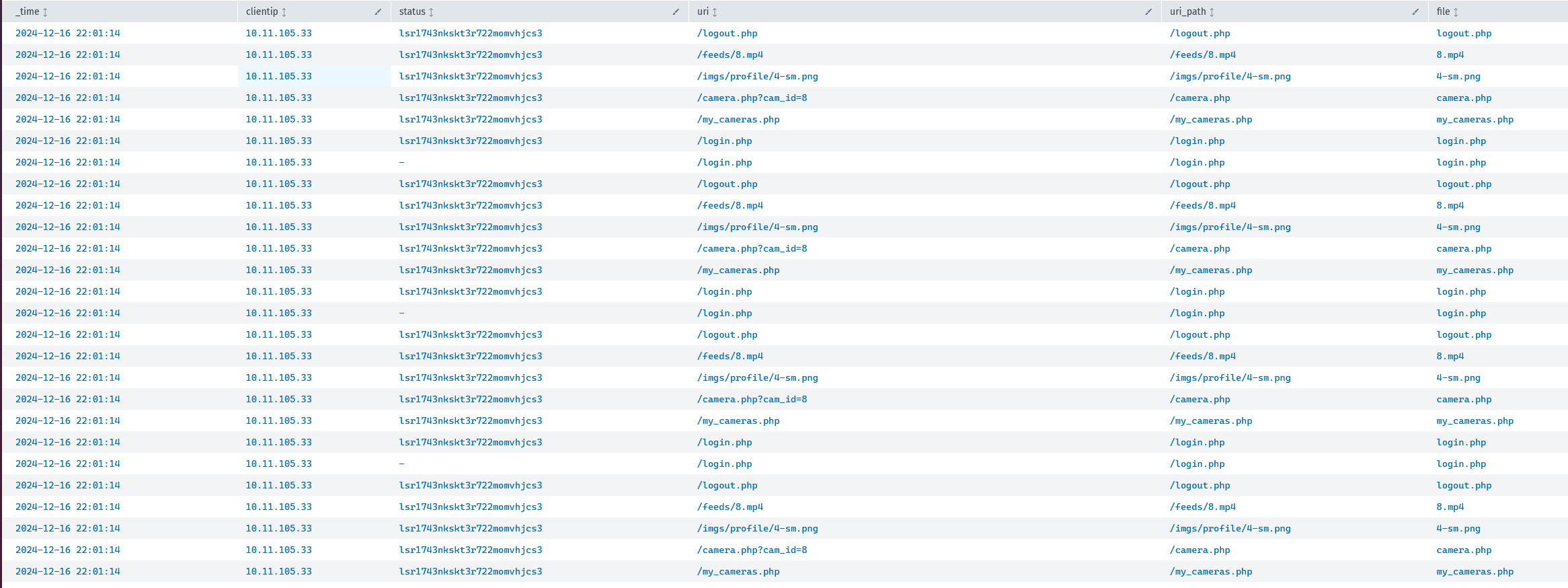
Searching through what the IP has done
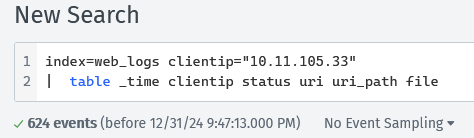 We can see there are a LOT of events (~600), and that the
We can see there are a LOT of events (~600), and that the session_id is completely different! Let’s go back and search through that id.
Finding out who was doing these actions:
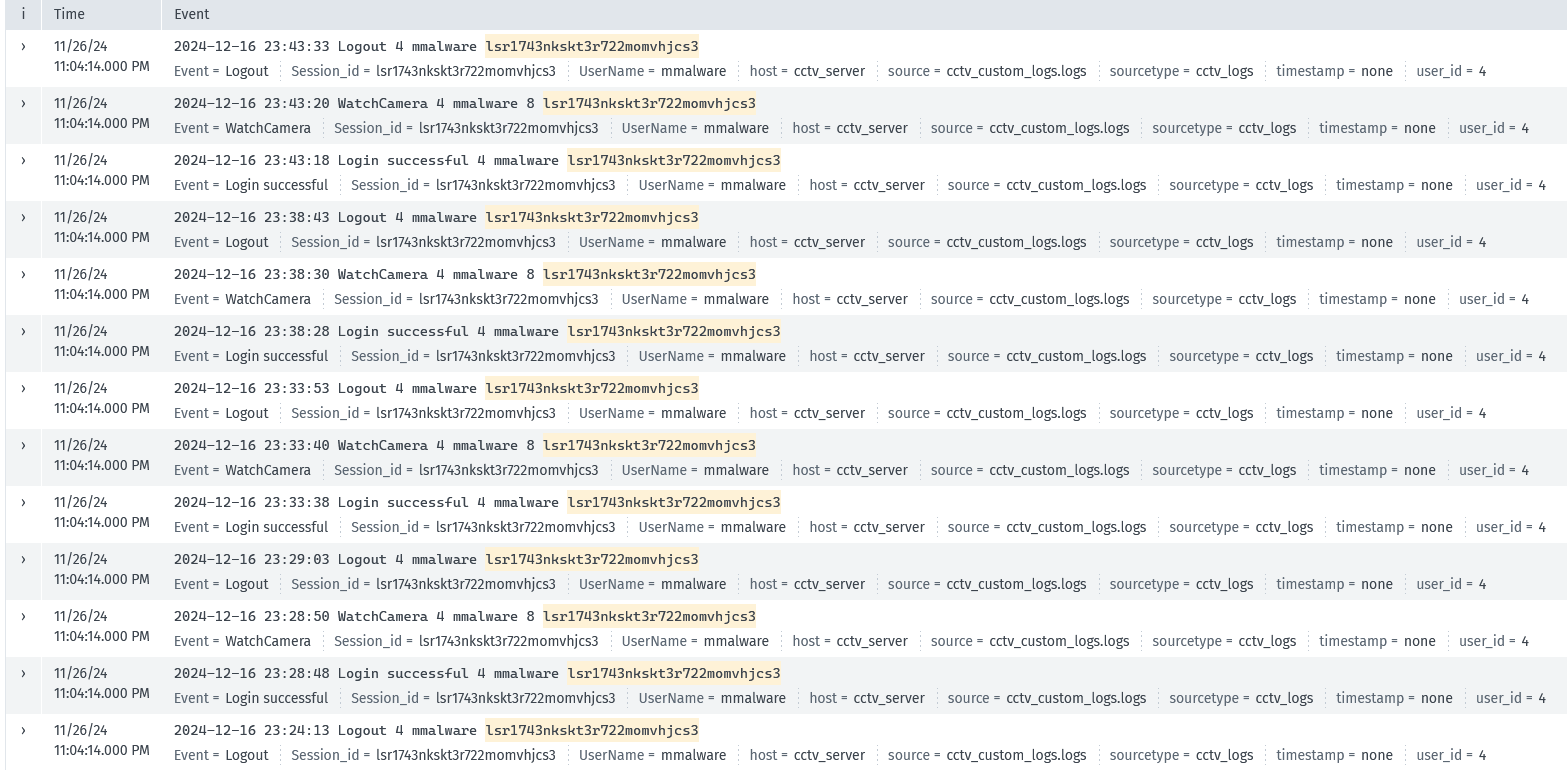 It was Mayor Malware all along! And his
It was Mayor Malware all along! And his user_id is 4.
We are done :)