Format String Attacks
API, like printf, has issues with exploits
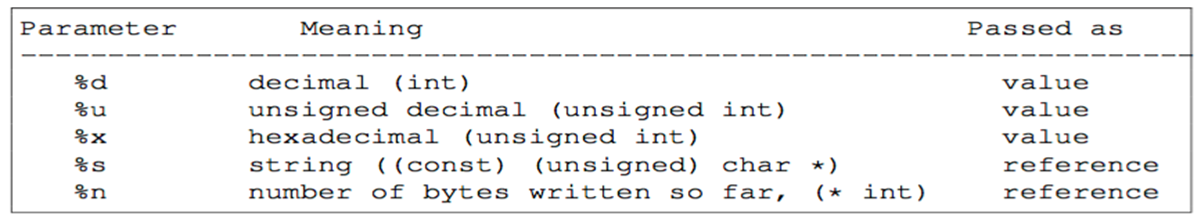
| Character | Description |
|---|---|
| d, i | Signed integer |
| u | Unsigned integer |
| f, F | Double |
| e, E | Double in normal form (think IEEE 754 floating point standard) |
| g, G | Double in scientific notation |
| x, X | Unsigned integer as a hex number |
| o | Unsigned int in octal (ya, octal, some people still want to know this) |
| s | Null terminated string |
| c | Character (char data type) |
| p | Pointer to void…depends on implementation. |
| n | Don’t print anything but write the number of characters successfully written so far into an int pointer |
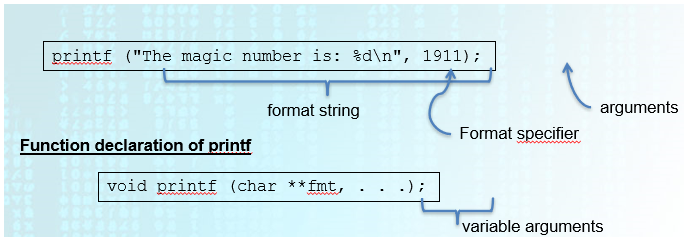
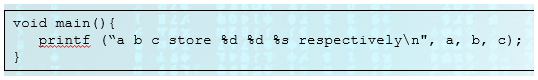
Invocation of printf
Insufficient Arguments to printf
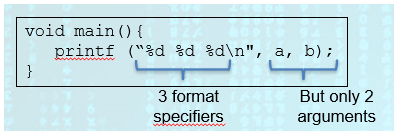
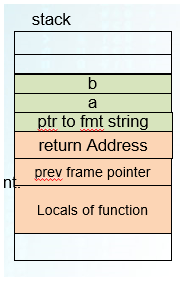
- In this case, once the program is done reading the
valueat memory addressb, it will continue to read what is on the stack (where the “cursor” left off). In this case it will print whatever value is above the memory address ofb.
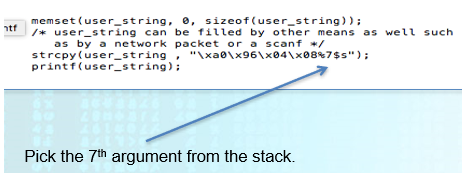
**Exploiting Inconsistent printf
Crashing a Program
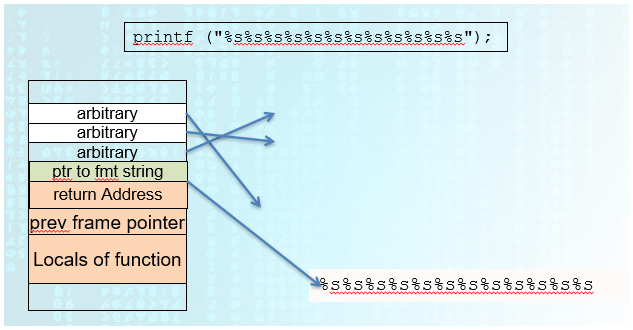
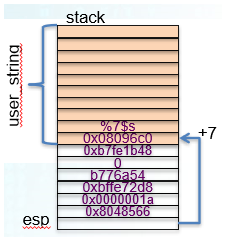
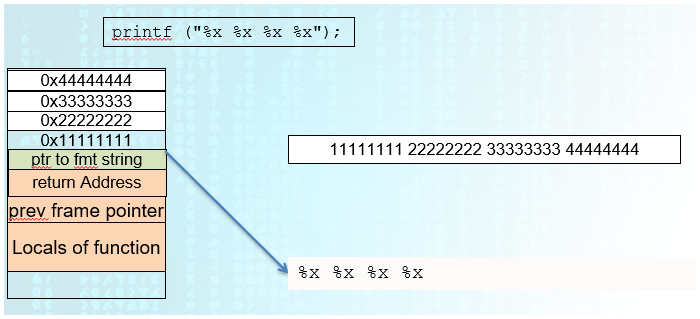
Printing Contents of Stack
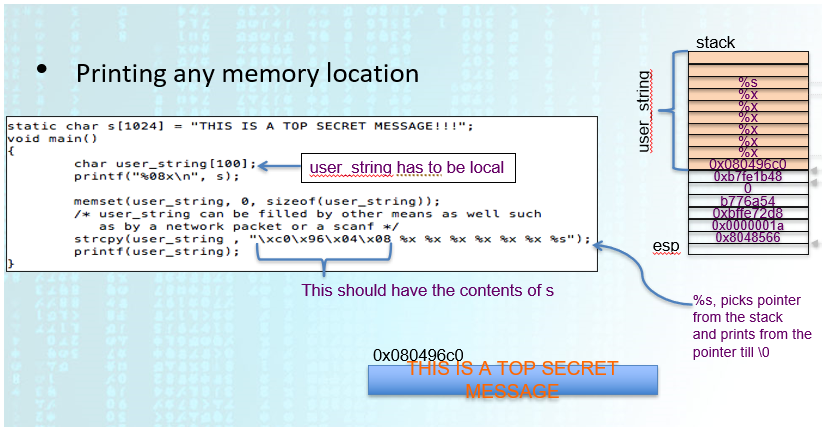
Printing any Memory Location
(1)
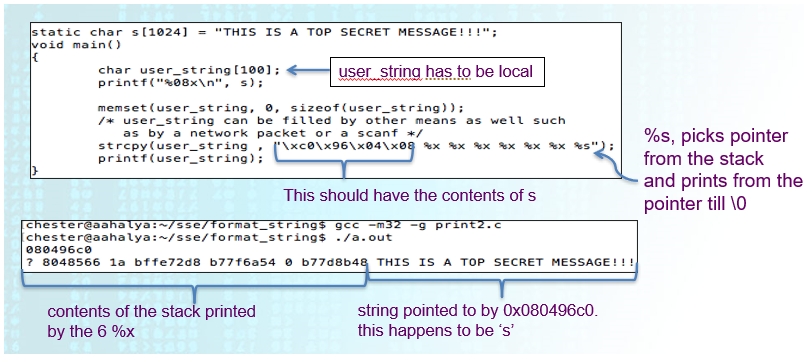
(2)
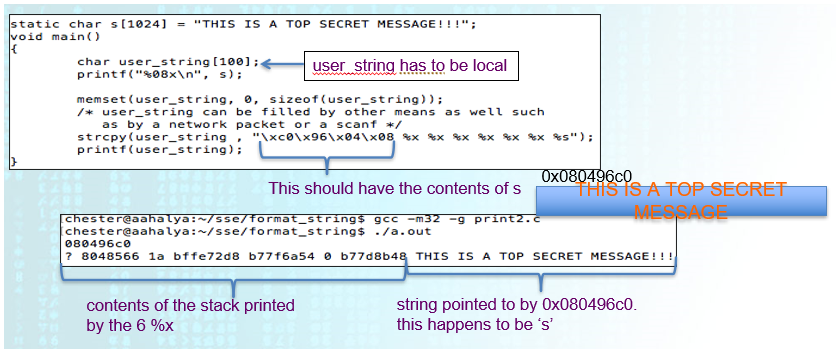
(3)
More Format Specifiers
- Reduce the number of
%xwith%N$s %nformat specifier:- Returns the number of characters printed so far.
iis filled with 5 here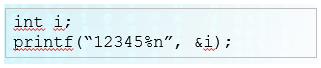
- Returns the number of characters printed so far.
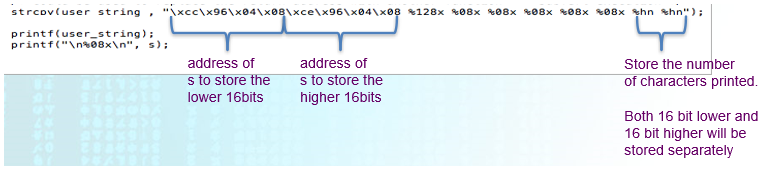
%hnformat specifier (Will only use 16 bits, can be used to store large numbers):- Used to write a short integer value into memory
- It takes the number of characters printed so far by
printfand writes that number, as a short integer, into a memory location that you specify as the target argument.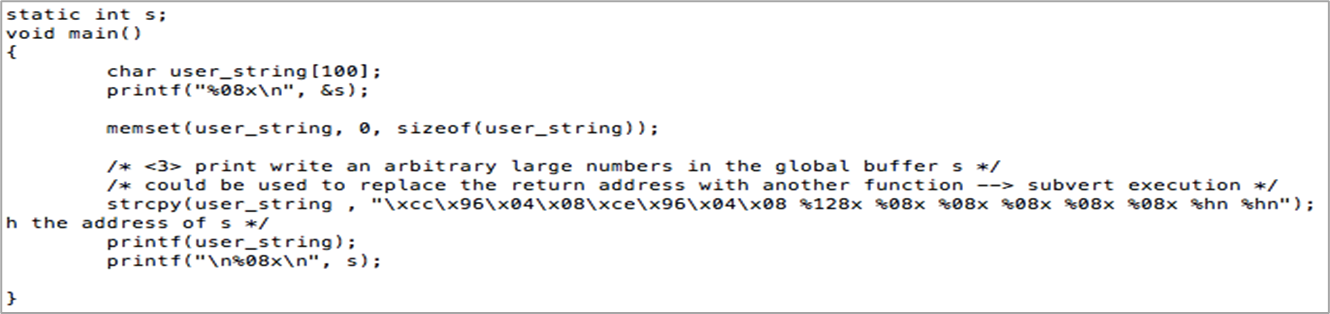
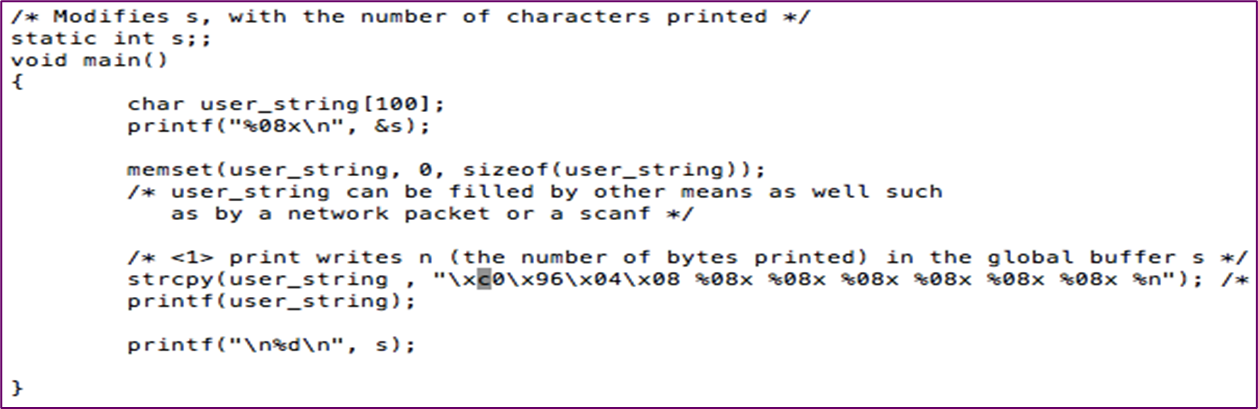
Overwrite an Arbitrary Location
- Using the same approach to read data from any location,
printfcan be used to modify a location as well- Can be used to change function pointers as well as return addresses
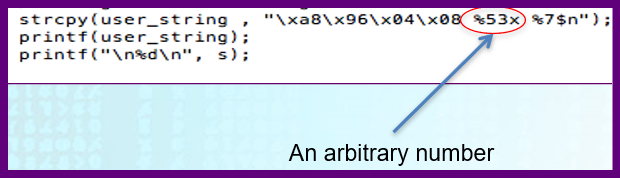
With some Number
With Arbitrary Number
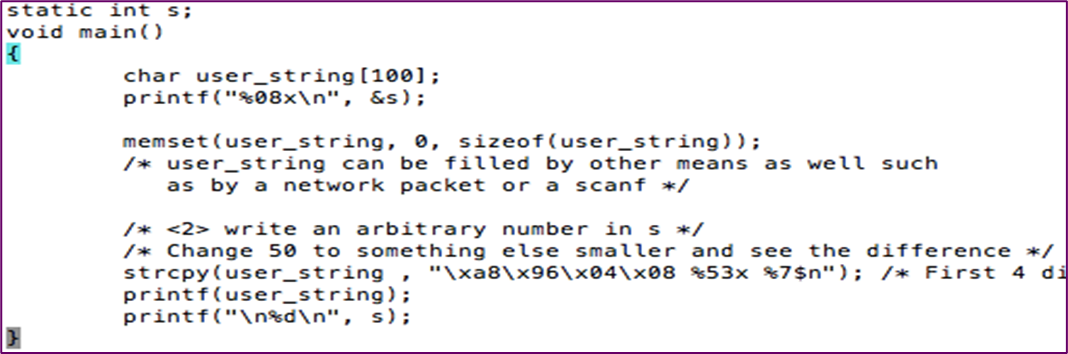
- Arbitrary number in this case is
%53x, as shown before%7$n
%n in printf
- There are 16 characters before
%n, so the value ofcwould be16.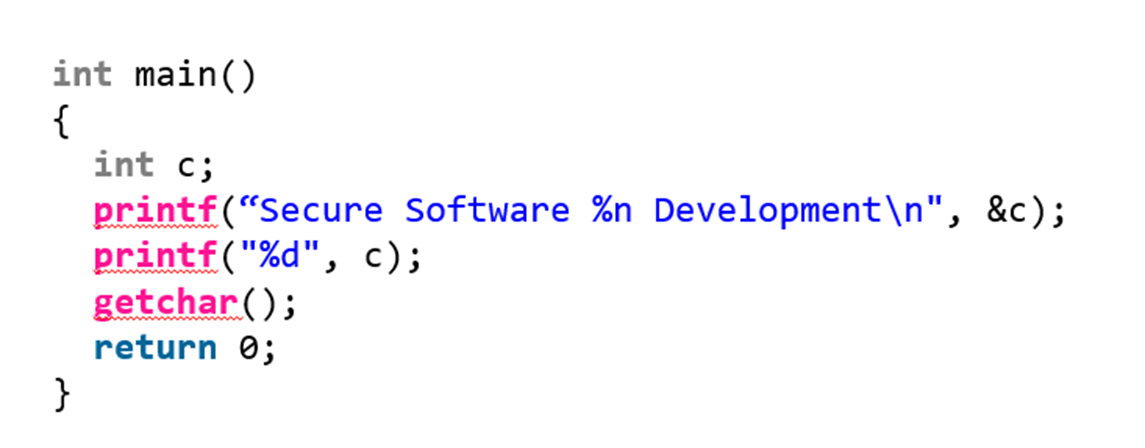
Recon
-
This basic level of reading stack data can be used for recon against a target program
-
Useful for reading usernames, passwords, return addresses, canary values, and other interesting data from the stack
-
What about using
%nspecifier to write arbitrary values in conjunction with the%0##xfunction used previously ???
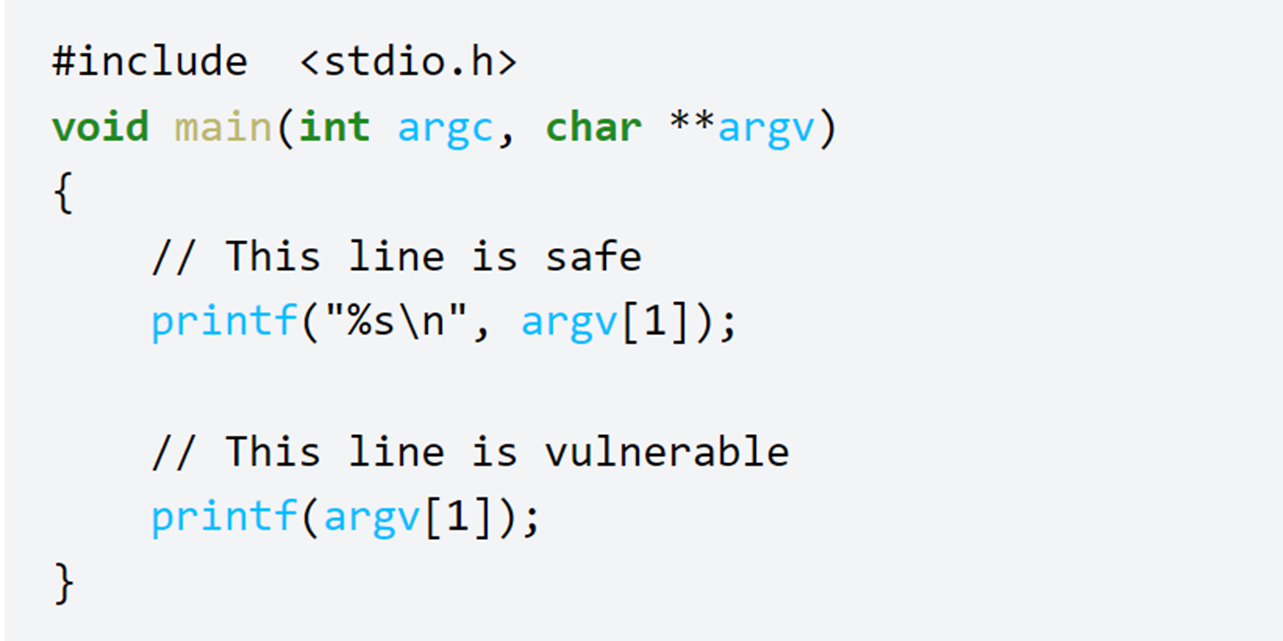
Safe Code for printf